Dark Web Marketplace Operator Arrested for Supplying Stolen Email IDs in Gujarat Bomb Hoax Case
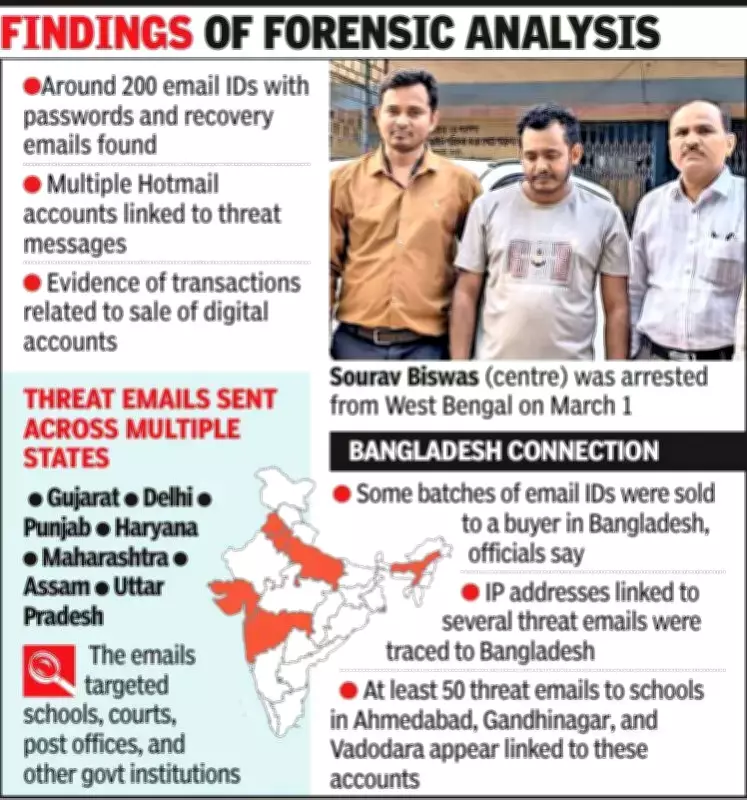
Ahmedabad: A dark web marketplace that sold stolen email accounts for as little as $1 each has been identified as a critical component in the chain of bomb hoax emails that terrorized schools, courts, and government institutions across Gujarat earlier this year. The individual allegedly operating this illicit platform, Sourav Biswas, aged 30, was apprehended from West Bengal on March 1 in a coordinated operation conducted by Ahmedabad's crime branch and cybercrime branch.
Biswas was transported to Ahmedabad on transit remand on March 3 and subsequently placed in police custody for intensive interrogation. According to cybercrime officials, Biswas supplied compromised email IDs to the perpetrators responsible for dispatching the threatening emails, which caused widespread panic and disruption throughout the state.
From Cybercafe Worker to Dark Web Entrepreneur
Biswas's descent into the dark web did not originate from a grand criminal scheme. He initially worked at a cybercafe before transitioning into digital marketing, where he promoted erectile dysfunction medications for a local pharmaceutical distributor. This role involved sending mass promotional emails to extensive recipient lists.
As his accounts were repeatedly blocked by recipients for spamming, Biswas began searching for fresh email addresses in bulk. His exploration led him to underground forums and dark web marketplaces, where he discovered he could purchase approximately 1,000 email accounts with passwords for about $100. A pivotal realization then transformed his activities: he recognized that other individuals also required these accounts. Consequently, he started reselling the same bundles for around $150, securing a consistent profit from the margin.
Systematic Expansion into Illegal Digital Trade
Over time, this side venture evolved into a more organized operation. Investigators revealed that Biswas constructed and managed a platform named expetseller.shop, which offered an expanding array of illegal digital goods and services. The site featured listings for hacked Gmail accounts, Google Voice numbers, social media accounts, compromised bank accounts, VPN and proxy services, remote desktop access, and valid phone numbers.
Biswas sourced compromised credentials from dark web marketplaces or leaked databases, modified the account details, and resold them. To obscure financial traces, payments were exclusively accepted in cryptocurrency, as confirmed by a cybercrime officer involved in the case.
Investigation Traces Bomb Threats to Dark Web Marketplace
The investigation into the bomb threats directed cybercrime officials to Biswas's digital operations. After schools, courts, post offices, and government institutions began receiving emails warning of bomb blasts—some containing provocative content referencing national leaders and seemingly designed to inflame tensions—investigators followed the digital trail through several compromised email IDs circulating online.
Technical analysis led them back to accounts procured through Biswas. IP addresses associated with at least 50 threatening emails sent to institutions in Ahmedabad, Gandhinagar, and Vadodara were traced to Bangladesh. Preliminary findings indicate that some of the email IDs sold by Biswas were acquired by buyers in Bangladesh, highlighting a potential cross-border dimension to the case.
Decoy Operation and Seizure of Evidence
To corroborate the illegal activities, cybercrime officials executed a decoy operation, posing as buyers interested in purchasing email accounts. This sting operation confirmed that compromised accounts were indeed being sold through Biswas's platform. A subsequent raid on his residence resulted in the seizure of three CPUs, five hard disks, and a cache of nearly 200 Gmail credentials.
An officer elaborated, "The sting helped establish that compromised accounts were indeed being sold through his platform. He was selling email accounts for $1-$5 each and accepted payments in cryptocurrency to avoid a financial trail."
Background and Legal Proceedings
Biswas, originally from Shri Palli Bazar in the Gobindpalli area of Barrackpore, North 24 Parganas district, West Bengal, is reported by police to have relocated to India from Bangladesh during the Covid-19 period in 2021. He settled near the India-Bangladesh border—approximately 8 kilometers from it, according to investigators—and obtained identity documents after his arrival. Authorities are currently verifying the legitimacy of these documents.
The case has been registered under Sections 43, 66, and 66C of the Information Technology Act, along with other applicable provisions. Given the possible cross-border implications, central agencies have been notified. Investigators are continuing to analyze the seized devices, map out additional buyers, and determine the full extent of the network involved in these cybercrimes.









