Dubai Authorities Sentence Three in Sophisticated Mobile Signal Hijacking Case
In a significant crackdown on high-tech fraud, Dubai authorities have prosecuted and sentenced three Asian men for operating a sophisticated mobile signal hijacking scheme that targeted unsuspecting residents in the upscale Dubai Marina area. Each defendant received a six-month prison term for their involvement in this elaborate scam, which came to light after numerous residents reported receiving unusual banking messages on their mobile phones.
How the Dubai Signal Hijacking Operation Worked
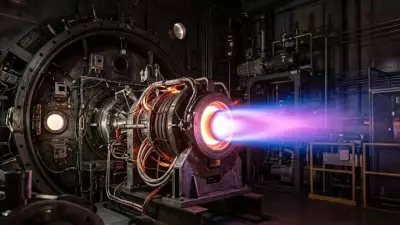
According to detailed records from the Dubai Criminal Court, the criminal group imported specialized equipment capable of jamming legitimate mobile signals and replacing them with a rogue frequency. This technical manipulation effectively created a fraudulent parallel network that automatically connected any mobile phone within its vicinity.
Once devices connected to this bogus signal, the system sent convincing fake SMS messages that appeared to originate from legitimate banks or official institutions. These texts featured authentic-looking language and logos, but contained malicious links designed to harvest personal and financial information. The criminals subsequently used this stolen data to siphon money directly from victims' accounts.
Police Investigation and Evidence Collection
Dubai Police forensic analysis successfully traced the fraudulent signal around Dubai Marina and Palm Jumeirah, eventually leading officers to a vehicle containing the sophisticated equipment. Inside the vehicle, authorities discovered jammers, signal receivers, and computers powered by improvised converters - all essential components for operating the fake network.
During court proceedings, the defendants denied any wrongdoing, claiming they were merely hired through Telegram messaging and paid to drive the vehicle or install the equipment. However, prosecutors presented a compelling digital trail that contradicted these defenses, and the court ultimately rejected their claims, ruling the evidence conclusive against them.
Legal Consequences and Official Response
The judges ordered the confiscation of all seized devices and decreed that the convicted men should be deported from the UAE after serving their prison sentences. Authorities have indicated that other individuals connected to this criminal ring remain at large, suggesting this operation may have been part of a broader organized crime network.
This case represents a relatively novel class of cyber-enabled fraud that goes beyond typical phishing or malicious SMS scams. By directly interfering with legitimate telecom infrastructure, scammers can bypass many layers of digital protection mechanisms that users and networks typically rely on for security.
Historical Context and Similar Incidents
This is not the first incident of its kind in Dubai. A similar episode occurred in 2024 when another group was caught transmitting a fake mobile network in the emirate, also using jamming devices to send phishing SMS links designed to install malware or compromise phone data. In that previous case, Dubai Police had similarly warned the public to remain vigilant about suspicious messages claiming to come from banks or government bodies.
These fraudulent devices, often called "fake base stations," mimic legitimate network tower signals and trick mobile devices into connecting to them. This connection allows cybercriminals to intercept sensitive data or redirect victims to fraudulent websites designed to steal credentials.
Rising Cybercrime Concerns in the UAE
Cybercrime remains a significant concern throughout the United Arab Emirates, despite robust law enforcement efforts. According to data from the UAE Cybersecurity Council, millions of attempted cyber attacks are blocked annually, with residents frequently targeted by various scams including phishing, hacking, "smishing" (SMS phishing), and investment fraud schemes.
Dubai Police and the Telecommunications Regulatory Authority consistently urge users to exercise caution regarding unsolicited messages or links, recommending that residents rely only on verified communication channels for financial or official correspondence. Officials have emphasized that even convincing messages featuring authentic logos and language can still be fraudulent if they originate from spoofed numbers or unexpected sources.
Protective Measures for UAE Residents
In response to this case and the increasing sophistication of mobile fraud tactics, cybersecurity experts recommend that UAE residents and visitors implement several key precautions:
- Avoid clicking links in unsolicited texts, even if they appear to originate from banks or government agencies.
- Verify sender information by contacting institutions directly using official contact details rather than responding to suspicious messages.
- Enable two-factor authentication (2FA) on all financial accounts and other critical digital services.
- Report suspicious messages or incidents through official UAE Police or e-crime reporting platforms.
These relatively simple security measures can significantly reduce the risk of falling victim to signal hijacking schemes or other forms of digital fraud.
The Broader Implications
The 2026 convictions in the Dubai Marina mobile signal hijacking case highlight the evolving nature of cybercrime in the region. The UAE continues to actively combat high-tech fraud that threatens residents' security and financial wellbeing. As criminals adopt increasingly sophisticated techniques to exploit mobile networks and digital trust, authorities are responding with coordinated policing efforts, legal deterrence measures, and comprehensive public awareness campaigns designed to educate citizens about emerging digital threats.
This case serves as a stark reminder that technological advancement brings both convenience and new vulnerabilities, requiring constant vigilance from both authorities and individual users to maintain digital security in an increasingly connected world.